How Crypto Drainers Are Using X (Twitter) to Target Web3 Users

Executive Summary
Crypto drainers have become one of the most damaging threats facing Web3 users today, siphoning millions of dollars from wallets across every major blockchain. As these operations have matured, so has the way they reach their victims, and X (formerly Twitter) has emerged as a primary vector for delivering malicious dApps to targeted victims at scale.
Blockaid has been tracking two major crypto drainer operations — AngelFerno and Rublevka. AngelFerno operates across multiple blockchains (EVM, Solana, TRON, XRP) using high-frequency automated posting through networks of accounts with artificially boosted follower counts, while Rublevka, a Solana-focused drainer, hides malicious links among legitimate reposts from verified crypto accounts to evade detection.
Both operations share the same foundational methodology: purchasing aged accounts for instant credibility, rebranding them with crypto terminology to trigger X's recommendation algorithms, obtaining Blue Checkmarks via paid subscriptions, and deploying malicious dApps disguised as airdrops or token claims, all using Cloudflare infrastructure for evasion.
What is a Crypto Drainer?
A crypto drainer is malicious code designed to steal cryptocurrency directly from victims' wallets. It is embedded into fake websites built to look like legitimate dApps, mimicking real projects, airdrops, and token claim pages to trick users into connecting their wallets. Once a user connects and signs a transaction, the drainer automatically siphons assets to attacker-controlled addresses, often within seconds and without the victim realizing until it's too late.
As demand for these tools has grown, so has their sophistication. Drainer developers continuously iterate on their code, incorporating AI to generate more convincing lures, evade security detection, and scale operations faster than ever, fueling the development of more advanced and harder-to-detect drainer tools.
What is Drainer-as-a-Service?
To understand crypto drainers and how their operations work at scale, it's necessary to first understand the underlying business model that powers them: the Drainer-as-a-Service (DaaS) model.

DaaS is a commercialized model for crypto theft that mirrors the structure of legitimate Software-as-a-Service businesses, complete with subscription tiers, technical support, and revenue-sharing arrangements, operating through two distinct layers of participants: the drainer developers who build and maintain the malicious infrastructure, and the affiliates who distribute the malicious dApps and drive victim traffic to them.
- Drainer developers are responsible for the technical foundation of the operation: They engineer the malicious JavaScript draining kits, the code embedded in fake dApps that, when a victim connects their wallet and signs a transaction, immediately siphons assets to attacker-controlled addresses. Beyond the core draining logic, developers maintain the backend infrastructure: smart contract interaction layers, wallet-scanning modules that prioritize high-value assets, evasion mechanisms (such as Cloudflare proxying), and technical support, including providing guides and managing dedicated Telegram communities.
- Affiliates own the operational role: they create and deploy malicious dApps based on infrastructure and templates provided by the drainer developers, then acquire victim traffic and direct it to those dApps. Traffic acquisition can happen in several ways:
- Independently - affiliates build their own distribution infrastructure from scratch: constructing fake social media personas, purchasing and rebranding aged accounts, and managing posting pipelines to drive organic-looking traffic to malicious dApps. Based on Blockaid's monitoring of drainer support chats and Telegram channels, the majority of drainer affiliates operate this way.
- Via Cybercrime Services - Affiliates may purchase dedicated distribution services offered within cybercrime forums, outsourcing specific aspects of their campaigns, including account boosting services to inflate follower counts, bot networks to manufacture social proof, or paid promotion through existing high-reach compromised accounts.
- Via Traffers - More sophisticated affiliates may recruit 'traffers', actors whose sole function is redirecting user traffic to malicious content.
In exchange, affiliates receive a percentage (usually 75-85%) of all funds stolen through their distributed links, with the remainder going to the drainer developers. This revenue-share model creates a powerful financial incentive structure that enables the operation to scale horizontally without the developers needing to manage distribution themselves.
Why Crypto Drainers Target X (Twitter) Users
X (formerly Twitter) provides drainers with a uniquely effective distribution platform, enabling threat actors to rapidly distribute malicious dApps disguised as legitimate airdrops and whitelist opportunities to highly targeted Web3 communities at scale.
Several features of the platform make it particularly attractive to attackers:
- Crypto-Native Audience Concentration - A dense population of Web3 users actively seeking airdrops creates a pre-qualified victim pool conditioned to click token-related links.
- Algorithmic Amplification - Engagement-driven algorithms prioritize viral content regardless of legitimacy, pushing scam posts into trending sections and recommendation feeds.
- Real-Time Virality - Posts spread instantly to thousands, allowing drainers to exploit time-sensitive events like token launches before victims recognize threats.
- Minimal Content Moderation - X allows seamless external URL sharing with preview cards and performs minimal automated phishing detection for crypto-related domains.
- Multi-Account Coordination at Scale - Networks of coordinated accounts (12+ identified) cross-promote links, creating illusions of organic consensus.
- Blue Checkmark Impersonation - Attackers create near-identical accounts mimicking legitimate projects and influencers, often obtaining verification through paid subscriptions for false credibility.
- Social Proof Trust Exploitation - Coordinated fake accounts artificially boost likes and retweets, making malicious posts appear community-endorsed and legitimate.
How Crypto Drainer Attacks Work on X (Twitter)
Blockaid has identified multiple drainer networks utilizing X as a primary infrastructure for distributing malicious dApps at scale. While these threat actors operate independently, they consistently employ a standardized set of tactics designed to exploit the platform's architecture and user trust.
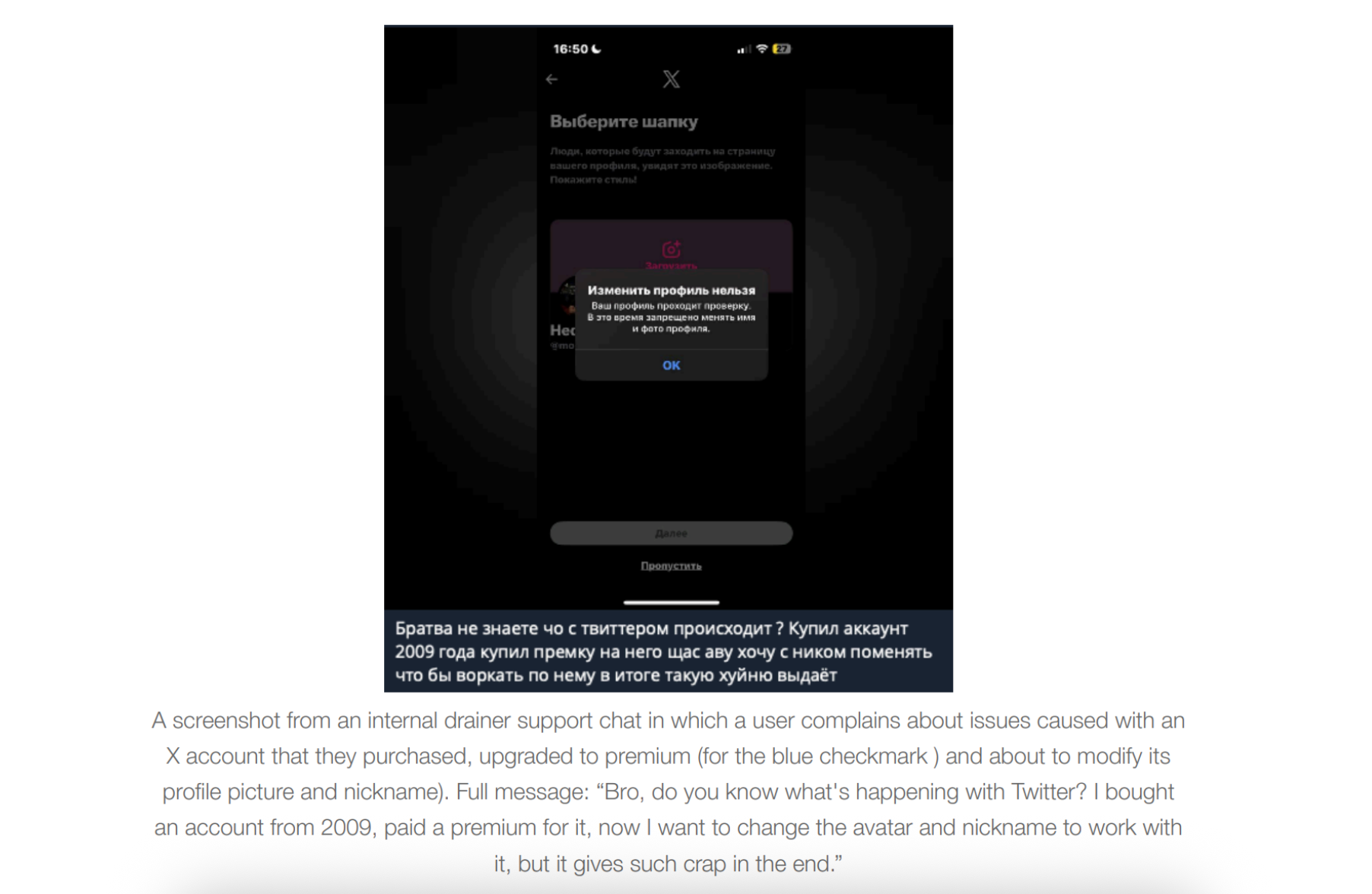
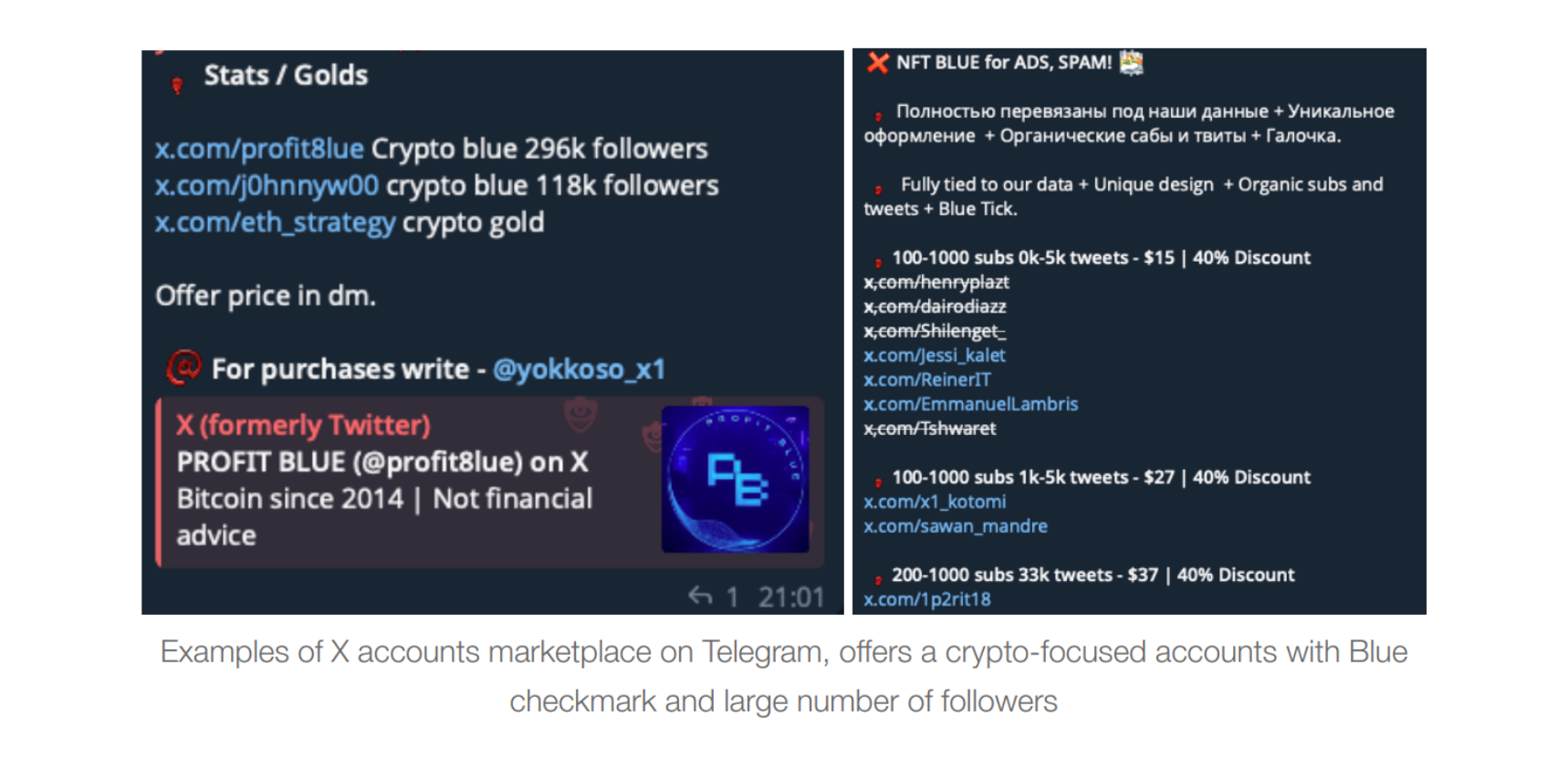
- Acquisition of Aged Accounts - To bypass automated security filters and establish immediate credibility, threat actors purchase established X accounts with an inflated number of followers through specialized marketplaces, including cybercrime forums and Telegram channels. Attackers specifically seek out accounts created 10 to 15 years ago to project an image of long-term reliability and seniority within the digital space.
- Rebranding for Web3 Relevance - Once an account is acquired, its profile is modified to align with the interests of the blockchain community. Attackers update usernames, bios, and profile pictures to include crypto-specific terminology — for example, adding ".eth" suffixes. These changes are designed to manipulate X's recommendation algorithms, increasing the likelihood that malicious posts appear in the "For You" feeds of targeted Web3 users.
- Exploitation of Paid Verification - Threat actors leverage X's subscription-based verification system to obtain "Blue Checkmark" status, providing a false veneer of legitimacy. Accounts are either purchased with existing verification or updated with a paid subscription immediately following the ownership transfer
- Manufactured Social Proof - Drainers exploit social proof by utilizing accounts with follower counts of 10,000–200,000. These inflated metrics are used to fabricate credibility, presenting the malicious actor as a high-authority industry veteran to lower the victim's skepticism.
- Automated Malicious Content Pipeline - After the account is configured and verified, it is integrated into an automated posting pipeline. Accounts are programmed to share new posts every few minutes, with content generated around trending industry topics — including fake airdrop campaigns and exclusive investment opportunities. Each post contains a direct link to a distinct malicious dApp. All identified malicious dApps within these pipelines utilize Cloudflare's infrastructure as a defensive layer to obfuscate their origin and bypass automated security tools, ensuring the malicious links remain active longer.
Which Crypto Drainers Are Targeting X (Twitter) Users
1. AngelFerno
AngelFerno is one of the largest and most prominent crypto drainers, offering variants for various chains including EVM, Solana, TRON, and XRP. In the campaign Blockaid tracked, multiple accounts were modified according to the playbook above and began sharing tweets containing malicious dApps at scale.
Each tweet follows a consistent template:
- Hook & Urgency - Every tweet begins with a high-impact statement to grab immediate attention, often using terms like "Big moves," "THIS IS HUGE," or "Revolutionary".
- Malicious Link - A direct URL to a malicious dApp is placed at the top of the post. These links often use domains that mimic legitimate projects (e.g., net-quant[.]network instead of the official quant[.]network) and are shielded by Cloudflare to evade security detection.
- The Lure - The text describes a fake value proposition, typically an airdrop, token claim, or reward.
- FOMO - The template includes fabricated claims of others successfully claiming large sums (e.g., "$500 to $15,000") to create urgency and fear of missing out.
- Brand Alignment - The closing text uses industry-specific jargon and mission-aligned language to build emotional resonance.
- Algorithmic Tags - Tweets conclude with a string of unrelated but trending crypto cashtags (e.g., $CRV, $ALLO, $SOL) to ensure the post is amplified by X's recommendation algorithms.
Blockaid detected 20 different X accounts, all with the same characteristics, sharing malicious AngelFerno dApps between September 2025 and January 2026. These accounts shared thousands of tweets containing 75 different malicious dApps. The high degree of similarity across accounts suggests either a single affiliate operating all accounts simultaneously, or multiple affiliates leveraging the same traffic distribution service, resulting in a near-identical operational fingerprint.
2. Rublevka
Rublevka is a major Solana-focused drainer that also utilizes X as a distribution vector through compromised Web3-branded profiles. The campaign appears to have begun in late 2025. On its official website, Rublevka provides its users with detailed instructions on how to drive victim traffic to malicious dApps through social engineering across multiple social media platforms — covering the full operational workflow from purchasing aged accounts, to modifying account characteristics, to warming up the account to simulate human-like activity using a VPN matched to the account's original location.
Blockaid detected more than 260 distinct URLs of Rublevka-associated dApps shared as part of this campaign.
While Rublevka shares the same foundational playbook as AngelFerno, it implements a different operational strategy designed to evade automated detection and appear more authentic to human observers:
- Lower-Profile Account Selection - Unlike AngelFerno's preference for high-follower accounts, Rublevka-associated accounts typically maintain follower counts ranging from several hundred to several thousand. Rublevka explicitly recommends avoiding inflating follower and like counts, claiming such practices risk immediate bans.
- Content Camouflage - Rublevka employs a technique where the majority of account activity consists of reposting content from legitimate blockchain entities, including major cryptocurrency exchanges and verified crypto influencers. Rather than high-frequency malicious posting, Rublevka accounts arbitrarily intersperse malicious dApp links between legitimate reposts, typically around 10 legitimate reposts followed by a single malicious post. This creates a human-like posting pattern that masks the account's malicious intent and extends operational lifespan.
- Template Consistency - When Rublevka accounts do share malicious content, they use the same structural template as AngelFerno, urgency hooks, direct malicious links, fake value propositions, social proof claims, and algorithmic hashtag exploitation.
For the full breakdown of AngelFerno and Rublevka, including IOCs and detected X accounts, read the complete threat intelligence report →
How Blockaid Protects Wallets from Crypto Drainer Attacks
As crypto drainer operations like AngelFerno and Rublevka grow in scale and sophistication, wallets are on the front line of protecting their users. Blockaid's End User Protection solution gives wallets the real-time intelligence and enforcement tools needed to detect and block malicious interactions before they can drain user funds.
- dApp Scanning - Real-time detection of malicious dApps, giving wallets the ability to surface a warning in the UI before a user connects to a malicious site.
- Token Scanning - Detection of malicious tokens associated with drainers, rugpulls, and scams, allowing wallets to flag harmful tokens and warn users before they interact.
- Address Scanning - Blockaid maintains real-time data on malicious addresses tied to drainer campaigns, allowing wallets to warn users before they send funds to a known malicious address.
AngelFerno and Rublevka are just two of the hundreds of active drainer operations Blockaid tracks. As new threats emerge daily, wallets need real time, always-on security that keeps pace before they impact your users.
Learn more about Blockaid's End User Protection →
About Blockaid
Blockaid is the onchain security platform trusted by the largest companies operating in Web3. Built by veterans of elite intelligence and cybersecurity units, Blockaid provides end-to-end protection for financial institutions, protocols, and end users — combining direct wallet and dApp integrations with real-time monitoring, detection, and response across smart contracts, infrastructure, and externally owned accounts. In 2024, Blockaid scanned over 2.4 billion transactions and blocked 71 million attacks. Blockaid is the security infrastructure behind Coinbase, MetaMask, Uniswap, Safe, and dozens of the most widely used platforms in the industry.
Learn more at blockaid.io, and follow us on Twitter and LinkedIn.
Blockaid is securing the biggest companies operating onchain
Get in touch to learn how Blockaid helps teams secure their infrastructure, operations, and users.


.jpg&w=3840&q=100)

